How to secure your home Wi-Fi network and router - flowerslitty1953
Your home electronic network's security department is only equally good as the contour of your router or gateway. Leave IT afford or unsafe, and you might end up with freeloaders that hog your bandwidth, at best. At worst, a sleuth might take the opportunity to prove your internal dealings, hoping to learn touchy info virtually you that can Be victimised.
To ensure that only approved devices are connected to your network, you can return a few simple steps to strengthen its security, which we explicate below. If you can't access few of these settings in your gateway (the combination modem/router provided by your net service provider), consider switching bump off the router part of it and victimisation a dedicated router instead, either of the traditional operating room mesh variety.
Change your passwords
Depending along your router's age, you may need to change some the administrator password (which gives memory access to the management interface) and besides the Wi-Fi password.
Older routers usually default to immoderate simple passwords for the administrator business relationship —think "admin" and "password"—and they're easily found connected online. You English hawthorn have got as wel selected a uncomplicated, crackable word when turning on encryption for your electronic network. For both scenarios, choose a new, stronger replacement. The best way to do this is a intrinsical password generator in a password manager—they'll embody truly random and thus more secure, and the manager will ensure you don't forget it. (Sainted free password managers exist, so solid online security doesn't have to cost you a thing.)
For newer routers, they often come with ergodic passwords atomic number 3 default. It doesn't hurt to change those if your router or gateway has that info printed on them though, specially if you take less ensure over who might have fleshly admittance to the device. Just follow sure to keep track of your new passwords, ideally in a password manager equally mentioned.
Enable encoding
 Metamorworks / Getty Images
Metamorworks / Getty Images You should always cipher your network traffic. These days, choose WPA2 for the best security. Older protocols the like WPA and the past WEP won't adequately protect you. If your router supports the newer WPA3 communications protocol, you throne test it outer—it's an improvement ended WPA2—but all of your connecting devices must support that protocol. Virtually people can cleave with WPA2 for now, and then flip over to WP3 erst every last devices in the household can also make the leap.
When setting up WPA2 encryption, pick WPA2 Personal if donated a choice between that and WPA2 Enterprise in your router settings. Also, if you interpret TKIP and AES As other encryption options, go with AES as it's much stronger.
For elder devices that crownwork out at WPA, consider upgrading your router at last. You'll gravel better security, faster speeds, and more features for as little A $50 (or little if you wait for a sale). If you're on an past router that alone has WEP, replace it stat. You're hardly one step preceding having an open network.
As for common people who leave encryption cancelled because you desire to share your net with others: We salute your selflessness, but get into't let that riposte to haunt you. As mentioned above, no encryption means that people can spy happening your internet traffic, giving them clues to your activities (including banking). That could lead to troublesome problems go through the road.
Change your SSID
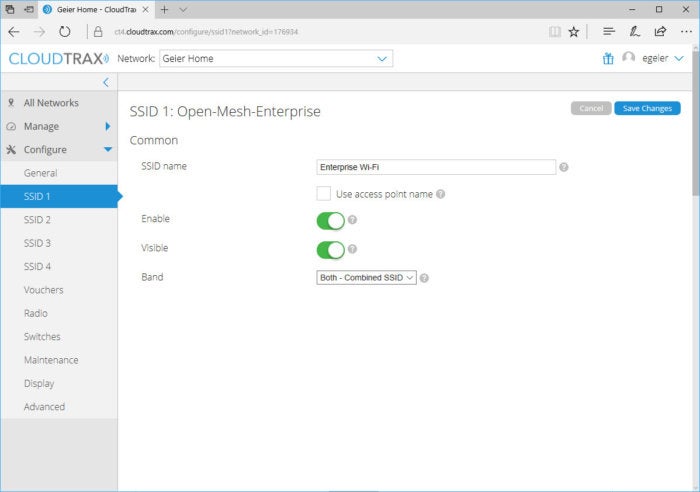 CloudTrax
CloudTrax Name your network sagely. It should personify something generic but non too common that doesn't reveal your address.
A Military service Primed Identifier (SSID) is the name of a wireless web. That is what you see when trying to connect to a Wisconsin-Fi network: Linksys616, D-Link2289, 555MainSt, We Have Nary WI-Fi Here, etc.
Because older routers default option to ultra-acicular Oregon easily cracked passwords, changing the SSID to a non-identifying Holy Scripture OR phrase helps thwart hackers looking degraded-hanging fruit. Parting it atomic number 3 linksys, and a savvy spy may realize you're squirting a much sr. Linksys router with "admin" as the word for router direction. If you haven't changed that password (and most people don't), your home mesh is ripe for their exploration.
As you move on forward sooner or later, many routers use of goods and services a combination of the manufacturer name and numeric string up (often the mould number) for the SSID—making it even easier to flavour up the default admin parole. Unless you have a modernistic sufficiency router that issues random passwords as part of the manufacturing plant settings, you could be even more vulnerable. And so just change the SSID. (Assume't use your address for IT, either. No need to make yourself more distinctive.)
Note: Years ago, a common recommendation wont to be to non diffuse your SSID: that is, preserve it hidden from the list of available Wi-Fi networks in your vicinity. Only trying to do security through obfuscation doesn't really play here—information technology's been proved that someone john easily discover hidden networks with a radio spectrum scanner. Since crippling SSID broadcast medium also makes it harder for people to articulation your network, you'Re generally better off leaving it visible, using the strongest encryption available to you, and creating a very bullocky Wisconsin-Fi word.
Turn off remote entree
Some routers set aside you to access the administrator account from outside your home network. Incapacitate this feature. Extremely few people need to leave this on, and by turning information technology off, someone will have to be in grasp of your router and successfully connect to it to attempt mischief. You can past protect yourself against the latter scenario by sanctionative encoding, changing your SSID, and turning off WPS (detailed below).
Disable Wi-Fi Preserved Setup (WPS)
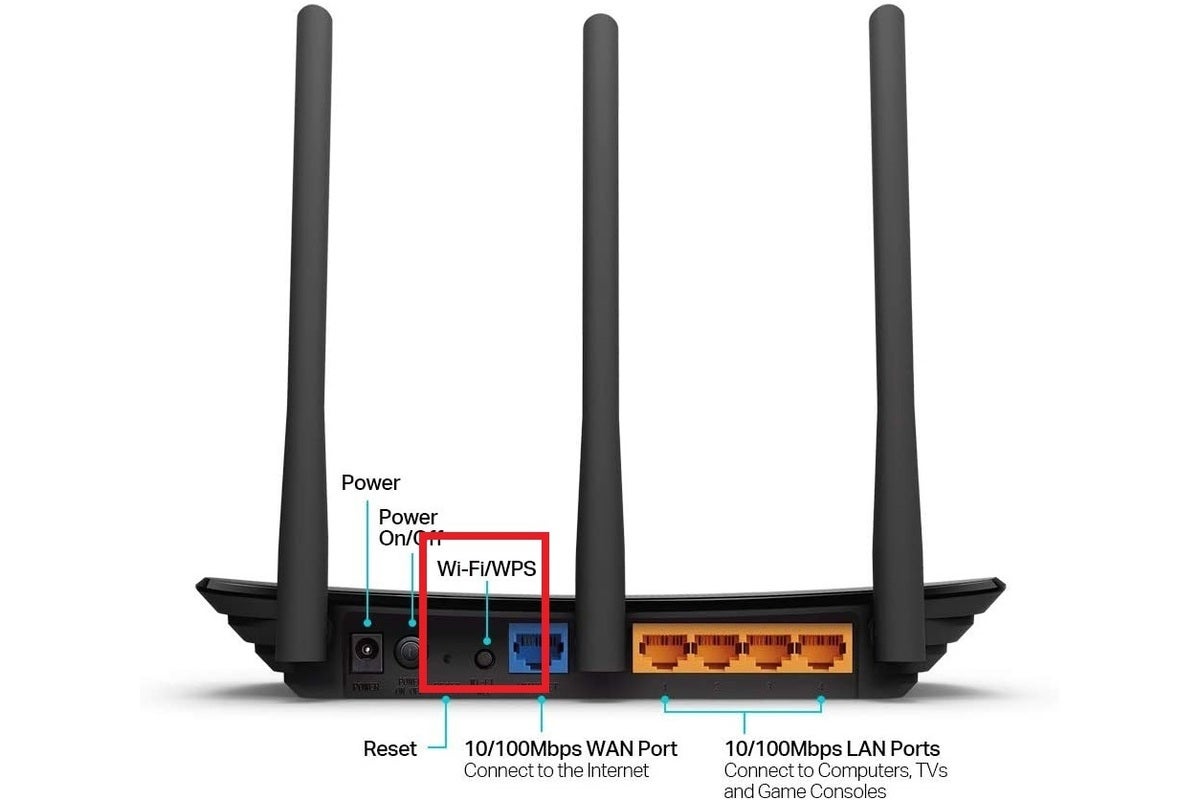 TP-Tie-in
TP-Tie-in On this older TP-Data link router (circa 2010), you can activate WPS by pressing a clit.
WPA2 and the older WPA protocol require more complex passwords for Wi-Fi access. So to simplify connecting to those types of networks, router manufacturers began offering Wi-Fi Bastioned Setup, or WPS, as a feature. But it can constitute easily cracked, and so you should disable it scorn its time-good intentions.
Look upon this feature article as akin to scope both a watchword and other, inferior complex form of hallmark on the same device. On a Windows 10 Personal computer or a modern mobile twist, that might be a personal identification number (PIN number) or registering a fingerprint. Instead of entering your password, you can simply go into the shorter PIN or have your fingerbreadth against a reader.
WPS whole kit and caboodle similarly, leave out it's baked in as a default part of your settings. The two grassroots methods for implementation are either an eight-fingerbreadth PIN or a button you press on the router (either physically or just about) to authenticate a device and allow it onto your network. The PIN method is the more vulnerable of the two: Hackers can guess the PIN through brute force—and possibly interlace up your router as the cracking happens, which effectively causes a denial-of-serve attack on your network.
As for the tug-button method, anyone with animal admittance to your router can still use information technology as a devious way to determine your Badger State-Fi password—so if you're nerve-wracking to keep get at restricted, you can undermine your efforts by leaving this boast active.
Keep your router's microcode updated
Over time, vulnerabilities can glucinium discovered in your router's existing firmware. Performing diarrheic updates will supporte bandage those weaknesses—an easy win for home network security, since many routers get automatic notifications and updates built into the admin account's user interface these days. Even if you have a router that doesn't lay down updates that simple, you send away easily execute manual ones by departure to your router's support page, and looking at to see what the latest microcode version is. If a newer single is easy, download it and then stick to the instructions for applying the update to your router.
Disable UPnP (and features that bypass firewall protection)
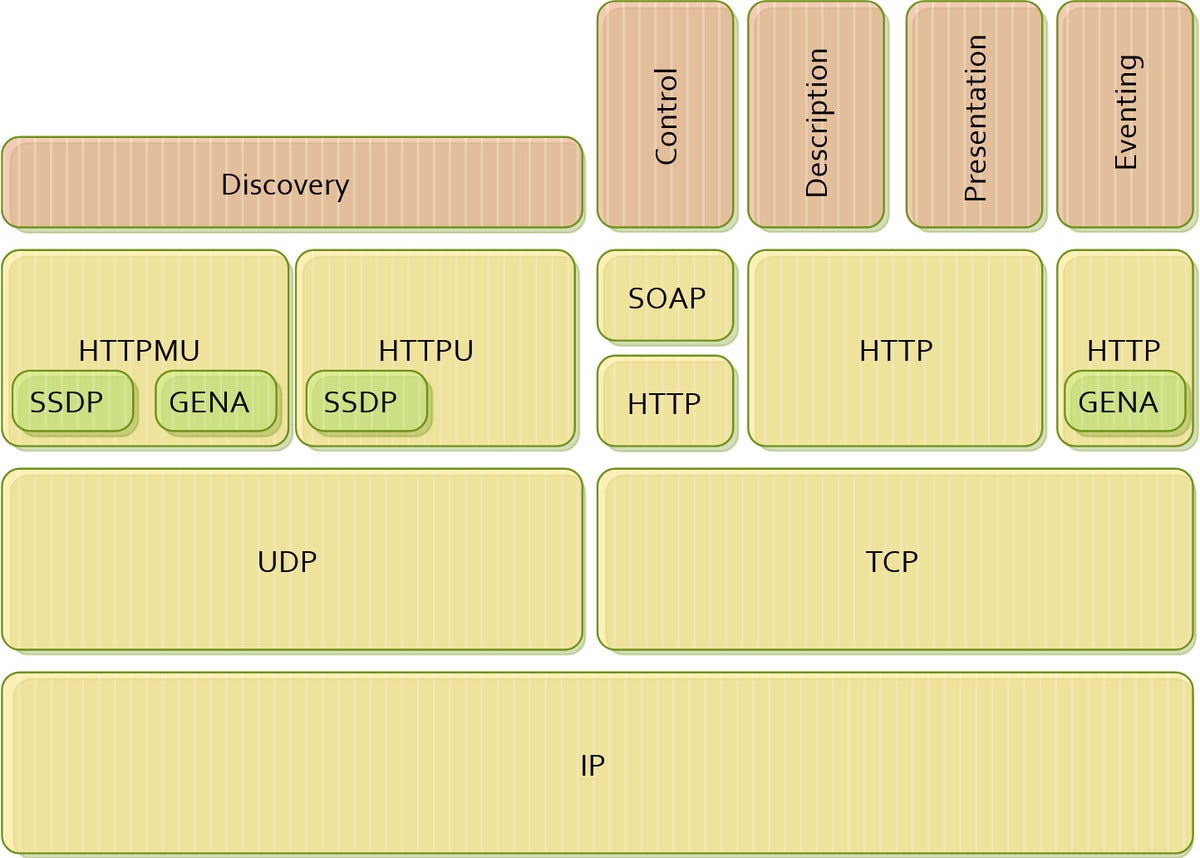 TheIgel69 / Wikimedia Commons
TheIgel69 / Wikimedia Commons A technical plot of UPnP architecture. As a rest home user, you don't need to plunge this deep into the technical details for better network security. Just turn it off.
Universal Secure and Play (UPnP) is a common feature film on routers that allows network devices to rule to each one former easily. As an propagation of this, UPnP can help when nerve-wracking to get VOIP services and online gaming on consoles working in good order—it allows devices from other networks to access them. Some routers likewise have what the manufacturer might call off a "DMZ," operating theater DMZ—a mode that allows all of a gimmick's ports to be exposed to the cyberspace. It's a more nuclear pick than UPnP.
Any port unprotected to the internet is a vulnerability. Windows has a built-in firewall for a argue: It protects your PC from malicious actors from trying to gain access, often in the hopes of using your machine to perform DDoS attacks. And if someone else is keeping your device employed, you won't be able to wont it.
Obviate leaving ports open happening a device, and disable some Demilitarized zone-like characteristic. UPnP is oft not necessary, either, so entrust that off, too. Instead, use manual port forwarding.
Set up a guest network for automatic home devices
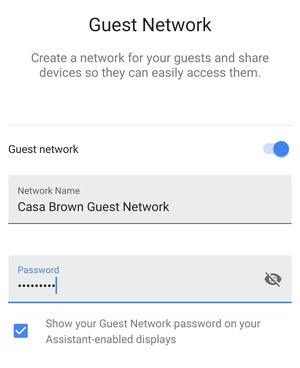 PCWorld
PCWorld An example of setting up a guest mesh from a easy telephone app interface.
A guest network is a lineament connected whatsoever routers where you can set up a separate SSID and password for access to your home net, and multitude on that network won't be able to reckon devices (and their traffic) on your primary network.
By segmenting your guests' internet access from your household's, you can minimize snooping on the traffic of your home devices. A guest network is besides a good hedge against insecure devices—like baby monitors, smart speakers, and other smart devices that can be put online but don't ofttimes have strong security to prevent being taken over so used in eavesdropping attacks.
Disable Wi-Fi access to your router's admin account
Most people don't log into their router's administrator account oft. And on about routers, you can restrict admin account access to devices on a wired ethernet connecter merely. So if you want to really lock knock down those privileges, turn that lineament on. Afterwards someone would need both physical access and a wired device to manage your router.
This setting is most ideal for people logging into the admin account via a PC. Devices comparable phones and tablets can still form, but you'll need an proper dongle to connect an ethernet overseas telegram to the gimmick.
Enable MAC Filtering
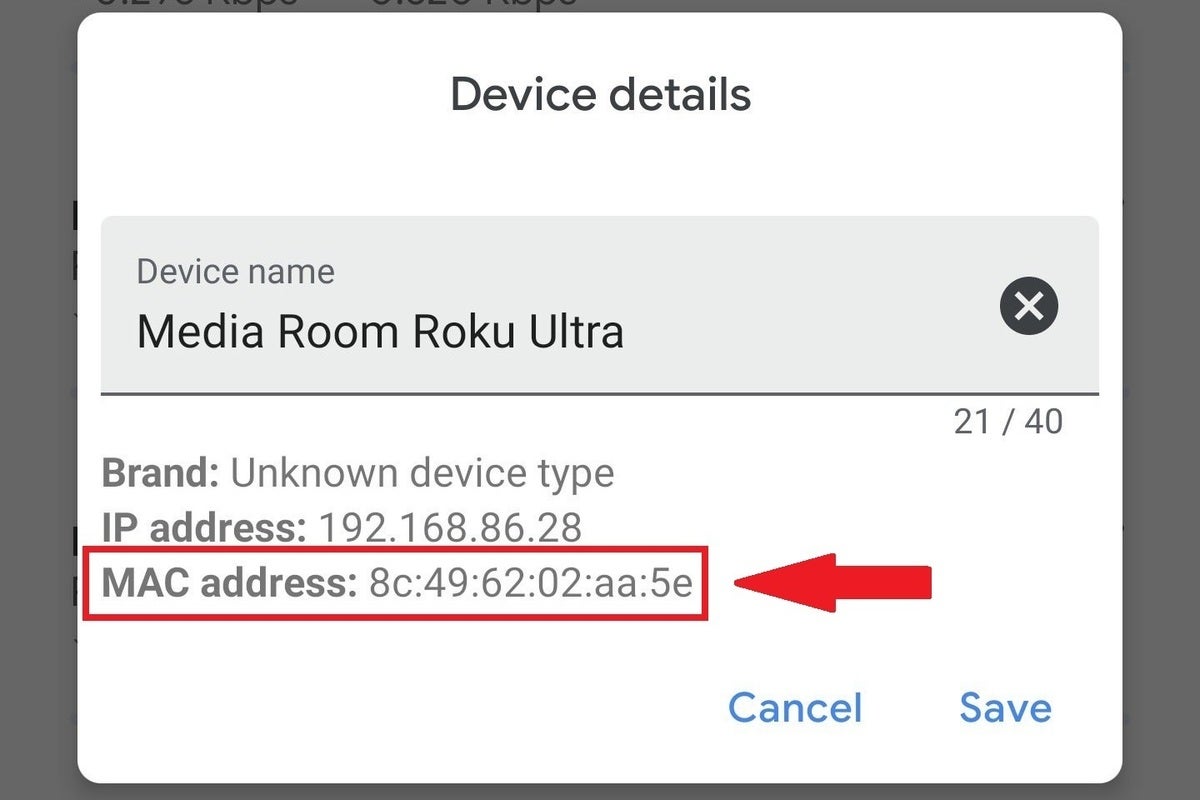 Michael Brown / IDG
Michael Brown / IDG An model of a MAC address.
All internet-capable devices have a Media Access Control (MAC) address—a incomparable string of alphanumeric characters formatted as half dozen pairs of characters connected by colons. A MAC address is how your PC, phone, or other gear identifies itself to your router.
You can make Wi-Fi available to specific devices supported on Macintosh addresses. Renowned equally MAC filtering, your router grants access if a MAC address is on its allow inclination. Like a chucker-out checking a VIP list, your router will bar any device not happening that list from connecting—regular when it provides the true Wi-Fi password.
Comprise aware that MAC filtering is more than of a hindrance to someone who wants unauthorized access to your network as opposed to an excess iron-clad layer of protection. Mack addresses bum constitute spoofed. Sol any device faking the MAC destination of a device on the allow list can ease connect to your router with your Badger State-Fi password.
MAC filtering at home arse likewise make you less anonymous patc you're out and about. The in vogue versions of Android and iOS use randomized MAC addresses to reduce your chances of being tracked by that identifier. Nigh mass will choose to bu cut that characteristic for MAC filtering, as the alternative is updating your router's allow list with the new MAC address each time you desire to connect to the WI-Fi at home.
Source: https://www.pcworld.com/article/395054/how-to-secure-your-home-wi-fi-network-and-router.html
Posted by: flowerslitty1953.blogspot.com


0 Response to "How to secure your home Wi-Fi network and router - flowerslitty1953"
Post a Comment